Introduction
Migrating VMware workloads to Azure through Azure VMware Solution (AVS) offers the best of both worlds—seamless scalability in the cloud while maintaining a familiar VMware environment. But with great power comes great responsibility, especially when it comes to Azure VMware Solution Security.
A well-structured security approach ensures that your infrastructure, applications, and data are protected against evolving cyber threats. Microsoft and VMware follow a shared responsibility model, where both parties handle specific security aspects. However, organizations must take proactive steps to secure workloads, enforce compliance, and protect against threats.
Let’s explore the key security measures that help safeguard your Azure VMware Solution (AVS) environment.
Understanding the Shared Responsibility Model for Azure VMware Solution Security
-
Security in the cloud is a team effort—Microsoft secures the underlying Azure infrastructure, while customers are responsible for protecting their own workloads, configurations, and compliance requirements.
How to Ensure Maximum Security?
- Collaborate with IT Teams, VMware, and Microsoft to clearly define roles and responsibilities.
- Use built-in security best practices from Azure and VMware to enhance your security posture.
- Stay compliant with security regulations using Microsoft’s built-in governance tools, ensuring Azure VMware security compliance at all levels.
Strengthening Compliance & Governance
Security isn’t just about firewalls—it’s also about governance and compliance. One misconfiguration or accidental deletion of a private cloud can lead to downtime, security breaches, or compliance violations. Strong Azure VMware compliance and governance strategies help prevent these risks.
Best Practices for Compliance and Governance:
✔ Apply Resource Locks – Prevent accidental deletions or modifications of critical resources. Locks can be applied at subscription, resource group, or resource level.
✔ Leverage Azure Arc – Extend Azure’s governance features to on-premises and multi-cloud environments.
✔ Use Azure Policy – Enforce security compliance across all AVS workloads, ensuring configurations meet regulatory standards.
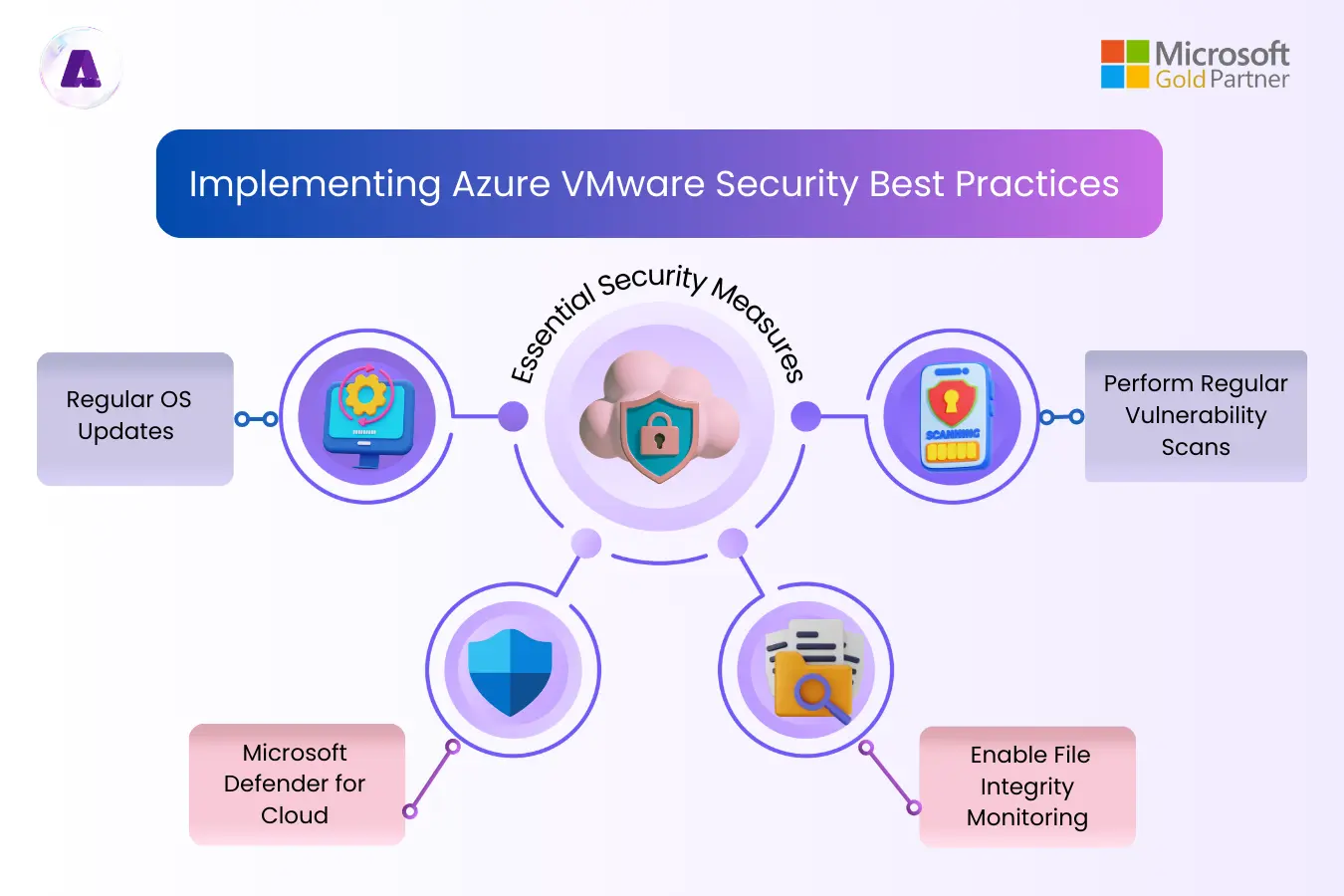
Protecting Guest Operating Systems from Cyber Threats
If your VMs are not patched or lack endpoint security, they can become an easy target for cyberattacks. Implementing Azure VMware solution security best practices ensures protection against modern threats.
2
Essential Security Measures:
🔹 Regular OS Updates – Keep systems patched to avoid vulnerabilities.
🔹 Microsoft Defender for Cloud – Protect against advanced threats like fileless attacks and security misconfigurations.
🔹 Enable File Integrity Monitoring – Detect unauthorized changes to critical system files.
🔹 Perform Regular Vulnerability Scans – Identify weak points in the system before hackers do.
By integrating Microsoft Defender for Cloud, organizations can benefit from real-time threat detection and automated security assessments.
Encrypting Data at Rest and in Transit
Data breaches are a nightmare scenario for any business. The best way to prevent unauthorized access is encryption.
Key Data Encryption Practices:
✔ Encrypt VMware vSAN Datastores – Use customer-managed keys for data-at-rest encryption.
✔ Leverage BitLocker – Encrypt guest VM disks to protect sensitive workloads.
✔ Enable Transparent Data Encryption (TDE) – Secure databases like SQL Server running on AVS guest VMs.
✔ Monitor Database Activity – Use built-in SQL Server Activity Monitor to detect suspicious actions.
Securing Network Traffic with Segmentation & Firewalls
Hackers often exploit network vulnerabilities to gain unauthorized access. That’s why network segmentation and firewalls play a critical role in Azure VMware Solution network security.
How to Strengthen Network Security?
✔ Use Network Segments – Isolate workloads logically to limit exposure to potential threats.
✔ Leverage VMware NSX-T Data Center – Enable micro-segmentation to restrict lateral movement within your network.
✔ Deploy Tier-1 Routers – Separate production, development, and testing environments to prevent cross-environment breaches.
✔ Use Intrusion Detection & Prevention Systems (IDPS) – Detect and block suspicious network activity.
With NSX-T micro-segmentation, organizations can create granular security policies to protect specific applications and workloads from unauthorized traffic.
Implementing Role-Based Access Control (RBAC) & Multifactor Authentication (MFA)
Unauthorized access is one of the leading causes of data breaches. Implementing strict access controls minimizes this risk and strengthens security solutions for Azure VMware Solution.
Best Practices for Access Management:
🔹 Use Role-Based Access Control (RBAC) – Assign access only to those who need it based on the principle of least privilege.
🔹 Enforce Multifactor Authentication (MFA) – Add an extra layer of security for critical system access.
🔹 Integrate Microsoft Entra ID (Azure AD) – Centralize identity management and take advantage of privileged identity management and conditional access policies.
🔹 Rotate Admin Credentials – Avoid using static passwords for VMware vCenter and NSX-T Data Center; instead, enforce regular credential rotation.
Monitoring Security and Detecting Threats
Continuous security monitoring helps detect threats before they escalate. Organizations should use Security Information and Event Management (SIEM) solutions to gain real-time visibility into their AVS environment.
Key Monitoring Strategies:
✔ Deploy Microsoft Sentinel – Aggregate logs and security events from Azure VMware Solution guest VMs.
✔ Use Defender for Cloud Alerts – Automate responses to security risks.
✔ Set Up Compliance Audits – Regular audits help identify weaknesses and ensure compliance with frameworks like HIPAA and PCI DSS.
✔ Automate Threat Responses – Use Microsoft Sentinel playbooks to streamline incident response.
By leveraging Microsoft Sentinel and Defender for Cloud, businesses gain deep threat insights and automated security workflows.
Final Thoughts: A Security-First Approach to Azure VMware Solution
Migrating VMware workloads to Azure provides unmatched flexibility and scalability, but security must be a top priority. By following these best practices, organizations can establish a resilient security framework that protects their cloud workloads against threats, data breaches, and compliance risks.
🔹 Understand your role in the shared responsibility model.
🔹 Use security tools like Microsoft Defender for Cloud and Sentinel.
🔹 Implement access controls, encryption, and network segmentation.
🔹 Continuously monitor, audit, and automate security responses.
By implementing these comprehensive security measures, businesses can ensure that Azure VMware Solution remains a secure, compliant, and resilient platform for mission-critical workloads.
For expert guidance and a seamless AVS migration experience, connect with Aptly Technology—your trusted partner in Azure VMware Solution deployment, security, and management.